The Ultimate Guide to Cryptographic Hashing
In the world of cybersecurity and data integrity, hashing algorithms are the unsung heroes. A "Hash" is essentially a digital fingerprint. It takes an input of any size—whether it's a simple password, a sentence, or a 10GB movie file—and produces a fixed-size string of characters. This output is unique to the input data; changing even a single comma in the original file will produce a completely different hash.
NexToolshub's Online Hash Generator allows developers, security researchers, and students to generate hashes instantly using the most popular algorithms. From verifying file downloads to understanding blockchain technology, hashing is fundamental to the modern web.
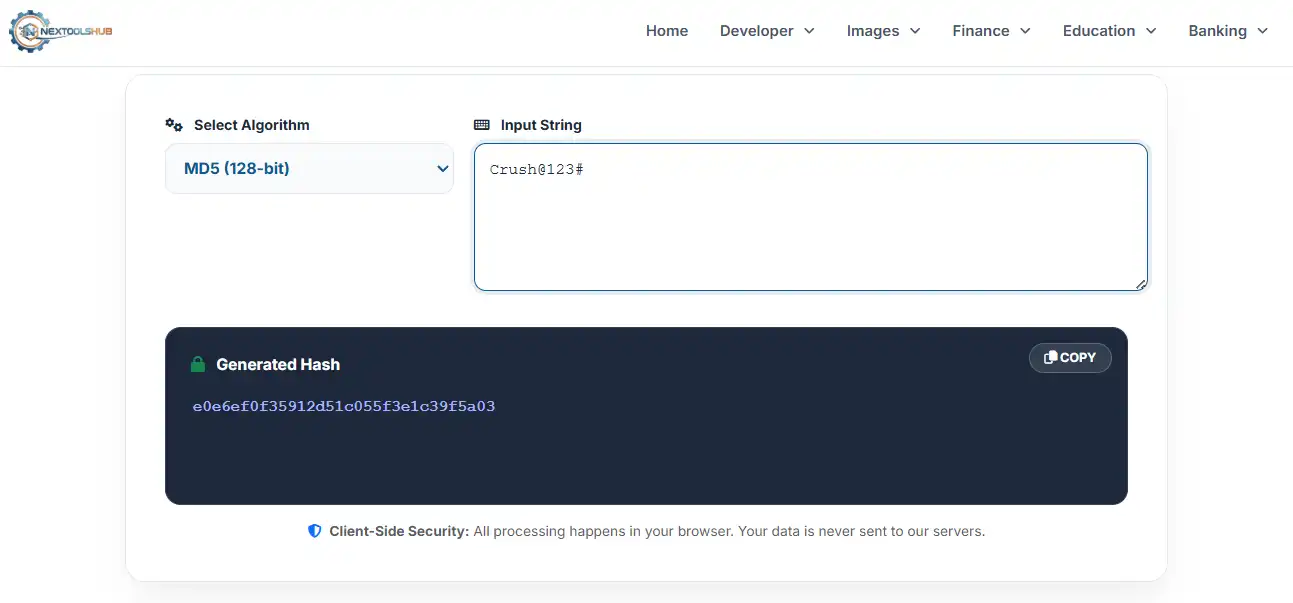
1. MD5 (Message Digest Algorithm 5)
MD5 produces a 128-bit hash value, typically expressed as a 32-digit hexadecimal number. Historically, it was used for password storage, but today it is considered **cryptographically broken**. Researchers have found ways to generate "collisions" (two different files producing the same MD5 hash).
2. SHA-1 (Secure Hash Algorithm 1)
SHA-1 produces a 160-bit hash value. Like MD5, it has been deprecated by major tech giants like Google, Microsoft, and Mozilla due to vulnerabilities. While stronger than MD5, it is no longer considered secure against well-funded attackers. It is still found in legacy systems and simple version control systems like Git (though Git is moving to SHA-256).
3. SHA-256 (The Gold Standard)
Part of the SHA-2 family, SHA-256 is currently the industry standard for security. It generates a 256-bit signature.
- SSL Certificates: It is used to secure HTTPS connections, protecting data between your browser and websites.
- Bitcoin: The entire Bitcoin cryptocurrency network relies on SHA-256 for mining and address generation.
- Password Storage: Modern applications hash passwords with SHA-256 (often with a 'salt') to keep them safe from hackers.
4. SHA-512 & SHA-3
SHA-512: Provides even higher security with a 512-bit hash. It is computationally faster on 64-bit processors compared to SHA-256.
SHA-3 (Keccak): The latest member of the Secure Hash Algorithm family. Internally, it works differently from MD5 and SHA-1/2 (sponge construction), making it resilient against attacks that might theoretically affect older algorithms.
Frequently Asked Questions (FAQ)
Common questions about hashing algorithms.